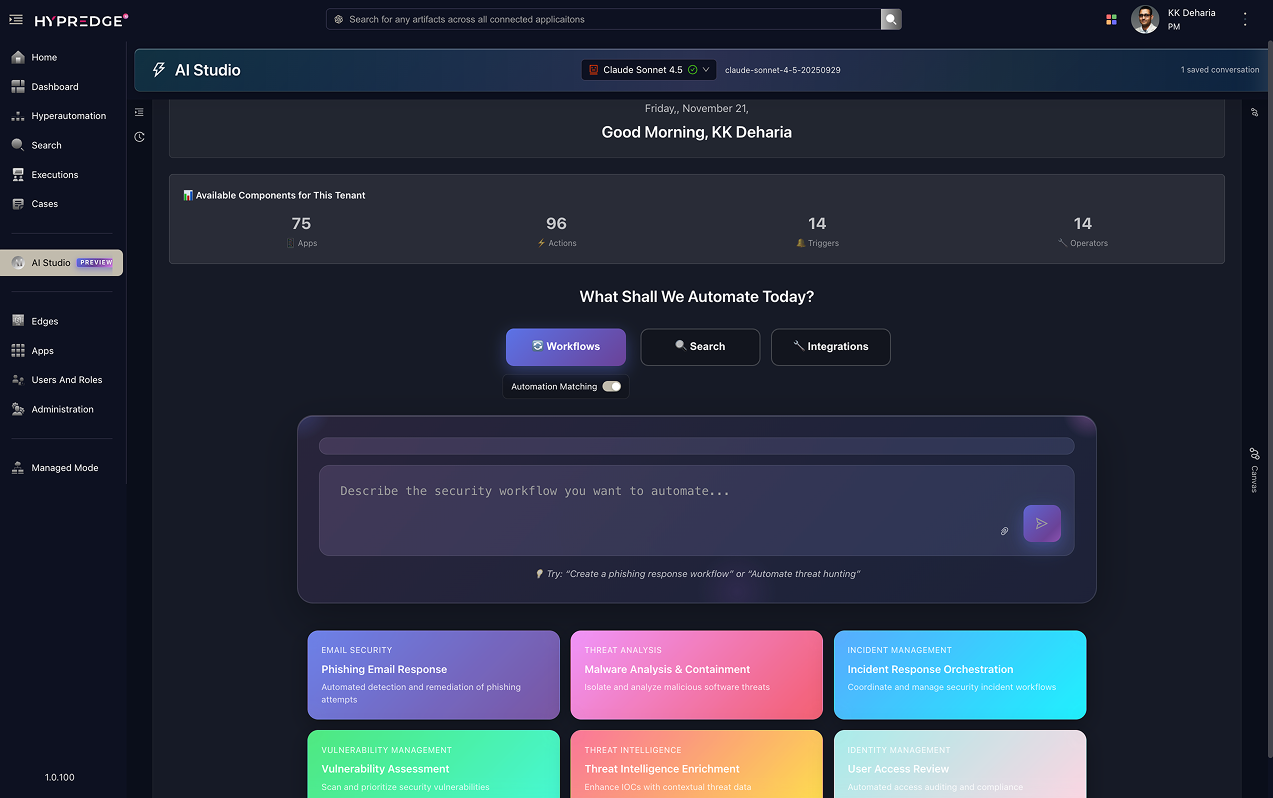
AI Studio
AI Generates, You Review & Deploy
Your AI-powered security operations center where AI handles the heavy lifting - generating playbooks, correlating threat intelligence, and building integrations.
AI Generates Playbooks, You Approve
Describe your security playbook in plain English. AI generates enterprise-grade automation with visual playbooks for your review - you validate, approve, and deploy with full visibility into every operator and connection.
How Playbook Generation Works
Our AI-powered playbook generator transforms natural language descriptions into production-ready security automations. Simply describe what you want to automate, and watch as AI builds a complete visual playbook with all the necessary operators, logic, and integrations.
Describe Your Playbook
Type your security automation need in plain English. Example: "When a phishing email is detected, analyze the sender, check VirusTotal for malicious URLs, quarantine the email, create an incident in BMC Remedy, and notify the SOC team"
AI Intelligent Matching
AI searches your existing playbooks first, suggesting pre-built automations that match your requirements. If none exist, it generates a brand new playbook tailored to your exact needs.
Visual Playbook Generation
Watch in real-time as AI constructs your playbook with visual nodes, operators, conditional logic, loops, parallel execution, and connections - all production-ready.
Why AI-Generated Playbooks
Playbook Generation Capabilities
Explore the powerful features that make AI playbook generation enterprise-ready
Smart Playbook Matching
AI searches your existing playbook library before creating new ones, recommending pre-built automations and preventing duplicate playbook creation
Enterprise Security
Role-based access control, audit logging, approval playbooks, encrypted secrets management, and compliance-ready playbook execution
14 Advanced Operators
HTTP calls, AI analysis, Database queries, Custom scripts, Conditional logic, For/While loops, Parallel execution, Query operations, Approval gates, User input, Wait/Delay, Break loops, Key-Value store, and Sub-playbooks
Visual Playbook Canvas
See your playbook come to life with node-based visual diagrams showing triggers, operators, actions, data flow, and connections in real-time as AI generates it
Production-Ready Export
Export playbooks as validated JSON with complete operator configurations, error handling, retry logic, and ready for version control and CI/CD integration
AI Correlates & Enriches, You Decide & Act
Ask questions in plain English - AI searches across all your security tools, correlates results, enriches threat intelligence, and recommends response actions. Security professionals decide which actions to execute with full context and control.
How Federated Query & Actions Work
Our AI-powered federated search breaks down tool silos by searching across all your security infrastructure simultaneously. No more switching between SIEM, EDR, firewalls, identity systems, and cloud platforms - one query searches them all, with instant action capabilities built in.
Natural Language Queries
Ask questions like "Show phishing emails from last week" - AI understands intent and translates to tool-specific queries
Parallel Multi-Tool Execution
AI queries 200+ tools simultaneously - SIEM, EDR, firewalls, cloud platforms - with real-time correlation
AI-Recommended Actions
AI suggests response actions - block, isolate, quarantine - you review and execute with one click
Convert to Automated Playbook
Transform any successful query into a reusable automation for future incidents
Why Federated Query & Actions

Take Immediate Actions on Query Results
No tool switching required - act directly from search interface
Federated Query Capabilities
Query across all your security tools with AI-powered correlation and enrichment
Automatic IOC Enrichment
Automatically enrich IPs, domains, URLs, hashes with threat intelligence from VirusTotal, AbuseIPDB, and multiple threat feeds
Network Traffic Query
Query network logs, firewall events, VPN connections, and DNS queries across security infrastructure with anomaly detection
Code & Configuration Query
Query source code repositories, configuration files, infrastructure-as-code, and API definitions across GitHub, GitLab, and internal repos
Identity & Access Query
Query users, groups, roles, permissions across Azure AD, Okta, Active Directory, and identity providers with real-time access analysis
Email & Communication Query
Query emails, messages, attachments across Microsoft 365, Gmail, Slack with phishing detection and malicious content identification
AI Generates Integrations, You Validate & Deploy
Describe what security tool you want to integrate - AI researches the API, generates complete integration specs, and produces production-ready code. Security teams validate, test, and deploy with full control over every integration.
How AI Integration Builder Works
Building security tool integrations traditionally takes days or weeks of API documentation review, authentication setup, and error handling implementation. Our AI Integration Builder does it all in minutes - researching APIs, generating tool-agnostic specs, and producing deployment-ready integrations automatically.
Describe What You Need
Tell AI what you want: "Build an AWS Security Hub integration" - natural language is all you need
AI Researches API Documentation
AI reads API docs, analyzes auth requirements, identifies endpoints, parameters, and error codes
Generate Tool-Agnostic Specs
Creates universal actions following ZS-Specs standards - no vendor lock-in
Complete Integration Package
Production-ready app definition, auth config, HTTP adapters, and documentation
Why AI-Powered Integration Builder

Integration Builder Capabilities
AI-powered tools to build production-ready integrations in minutes
Production Deployment Ready
Creates deployment-ready JSON specs following ZS-Specs standards with full validation, testing hooks, error handling, and comprehensive documentation
Multi-AI Provider Support
Choose your preferred AI: Claude (Anthropic), GPT-4 (OpenAI), Gemini (Google), or Ollama (local) - switch providers based on your needs
Tool-Agnostic Design
Creates universal actions (like "get file reputation") that ANY security vendor can implement - avoiding vendor lock-in and enabling interoperability
Multi-Auth Support
Full support for OAuth2, API keys, bearer tokens, client credentials, SAML, and custom authentication schemes with secure credential management
HTTP Adapter Auto-Config
Automatic HTTP adapter setup with proper request/response mapping, headers, error handling, retries, timeouts, and pagination support
Ready to Transform Your Security Operations?
Experience AI-powered playbook generation, federated search, and integration building. Let AI handle the heavy lifting while you maintain full control.